Security Reviews Are Not About Badges
Security reviews are rarely about what marketing teams think they are about.
They are not impressed by a compliance badge on the homepage. They are not reassured by phrases like “enterprise-grade” or “industry standard.” IT teams walk into vendor reviews with a very specific goal: to understand how the system is actually built, how control is enforced, and how risk is handled when something goes wrong.
Across industries, the questions tend to be remarkably consistent. How are tenants isolated? How is encryption managed? What do audit logs really capture? What happens to our data when we leave?
The difference between a surface-level answer and a confident one is not tone. It is specificity.
This guide breaks down the 10 security questions IT actually asks during vendor reviews and what strong, engineering-grade answers sound like, so buyers can separate polished claims from real architecture decisions.
The 10 Questions IT Actually Asks
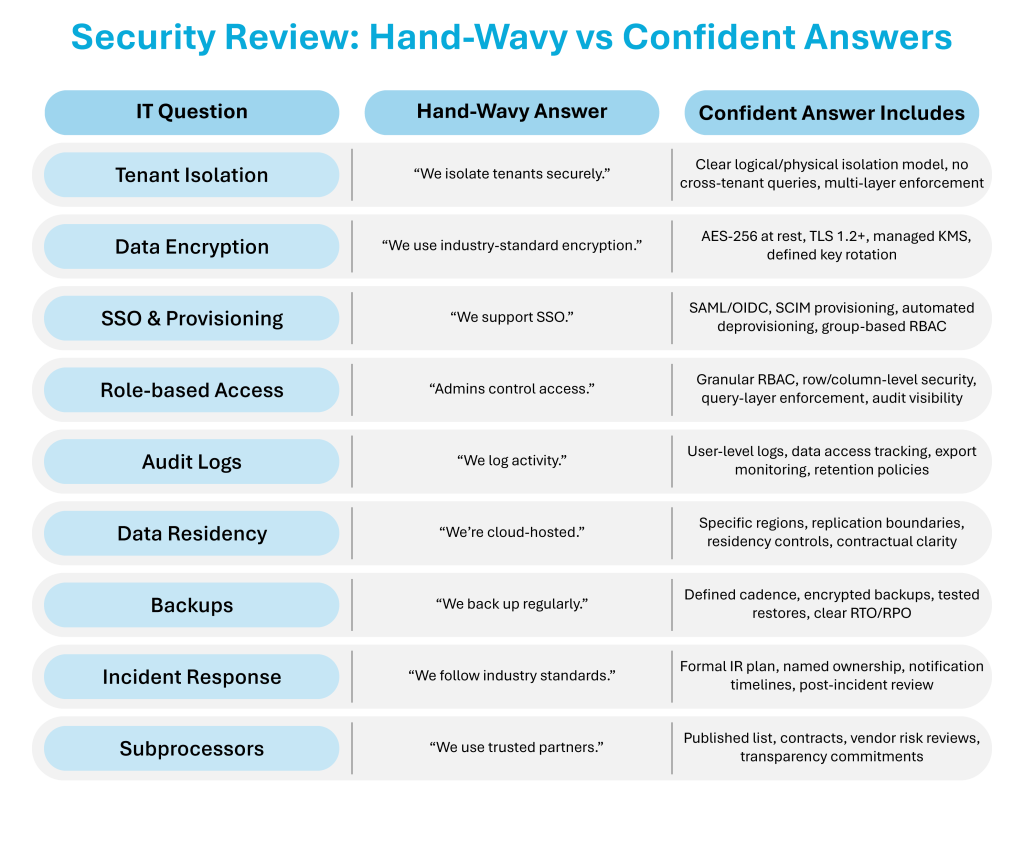
1. How Is Tenant Isolation Enforced?
What IT is really asking: Can one customer’s data ever leak into another’s?
Hand-wavy answer: “We isolate tenants securely.”
What a confident answer includes:
A clear explanation of logical versus physical isolation. Dedicated schemas or strict row-level isolation. Enforcement at multiple layers, including application and query level. Explicit confirmation that there are no cross-tenant query paths. Clarity about how shared infrastructure is segmented and tested. Strong answers describe architecture, not reassurance.
2. How Is Data Encrypted?
What IT is really asking: How is data protected at rest and in transit, and who controls the keys?
Hand-wavy answer: “We use industry-standard encryption.”
What a confident answer includes:
AES-256 encryption at rest. TLS 1.2 or higher in transit. Managed key services such as cloud KMS. Clear key rotation policies and separation of duties. Strong answers distinguish between encryption mechanisms and key management practices, because encryption without disciplined key control is incomplete protection.
3. How Do You Handle SSO and User Provisioning?
What IT is really asking: How tightly does identity integrate with our existing controls?
Hand-wavy answer: “We support SSO.”
What a confident answer includes:
Support for SAML 2.0 or OIDC. SCIM-based automated provisioning. Deprovisioning tied directly to the identity provider. Group-based RBAC mapping that reflects enterprise roles. Specificity about how user lifecycle events propagate. Strong answers demonstrate automation, not manual onboarding workflows.
4. How Is Role-Based Access Enforced?
What IT is really asking: Are permissions granular and consistently applied?
Hand-wavy answer: “Admins can control access.”
What a confident answer includes:
Granular RBAC with clearly defined roles. Row-level and column-level security where required. Enforcement at the query layer, not just at the interface. Separation between object-level and data-level controls. Audit visibility into access decisions. Strong answers explain how access is enforced technically, not just configured administratively.
5. What Do Audit Logs Actually Capture?
What IT is really asking: Can we reconstruct who did what, and when?
Hand-wavy answer: “We log activity.”
What a confident answer includes:
Timestamped, user-level logs. Capture of login attempts, data access events, exports, and administrative actions. Download tracking. Clear retention policies. Exportable logs for compliance review. Strong answers show that logs are actionable, not just stored.
6. Where Is Data Stored and What About Residency?
What IT is really asking: Where does our data physically live, and does it ever move?
Hand-wavy answer: “We’re cloud-hosted.”
What a confident answer includes:
Specific hosting regions. Clarity on residency controls. Defined replication boundaries. Transparency about cross-border movement. Contractual commitments on data location where applicable. Strong answers remove ambiguity about geography and jurisdiction.
7. How Are Backups Handled?
What IT is really asking: Can we recover safely and predictably?
Hand-wavy answer: “We back up regularly.”
What a confident answer includes:
Defined backup cadence. Encrypted backups. Clear RTO and RPO commitments. Regular restore validation testing. Documentation of recovery procedures. Strong answers show that backups are tested, not assumed to work.
8. What Is Your Incident Response Process?
What IT is really asking: What happens when something goes wrong?
Hand-wavy answer: “We follow industry standards.”
What a confident answer includes:
A defined incident response plan. Named ownership and escalation procedures. Clear customer notification timelines, typically within 24 to 72 hours. Post-incident review processes. Strong answers describe operational readiness, not generic alignment with standards.
9. Do You Use Subprocessors or Subcontractors?
What IT is really asking: Who else touches our data?
Hand-wavy answer: “We use trusted partners.”
What a confident answer includes:
A published subprocessor list. Contractual agreements with security obligations. Vendor risk assessments. Transparency commitments for changes. Strong answers acknowledge dependency risk and show how it is managed.
10. What Happens When We Leave?
What IT is really asking: How is our data handled at termination?
Hand-wavy answer: “Data is deleted per policy.”
What a confident answer includes:
A clear deletion window. Defined backup purge cycles. Written confirmation or certificate of destruction. Transparency about residual log retention where applicable. Strong answers explain the offboarding lifecycle in detail, not just the intent to delete.
Conclusion: Does Your Security Review Sound Like Security or Marketing?
Security reviews are not adversarial. They are alignment exercises between how a system is built and how it will be used.
Strong vendors answer security questions with architecture, not adjectives.
Certifications like SOC2 are baseline. They signal process maturity, not implementation depth. What separates surface-level compliance from engineering discipline is specificity. Confident vendors explain mechanisms. They describe enforcement layers. They name ownership. They clarify how controls operate in real scenarios, not just in policy documents.
Vague language often signals that security is treated as a checklist. Specific language signals that it is built into the system.
At SplashBI, enterprise-grade controls are part of the architecture, not an afterthought. Our teams are comfortable in real security reviews because the answers are grounded in engineering decisions.
If you want direct, detailed answers, reach out to our security experts.