The Deployment Debate That Never Ends
IT deployment conversations often start with strong positions.
“We need it on-prem.”
“We only deploy cloud.”
The debate is usually framed around security and control. On-prem can feel safer because systems sit behind the company firewall. Cloud can feel safer because providers invest heavily in infrastructure security and resilience.
But location alone does not determine security.
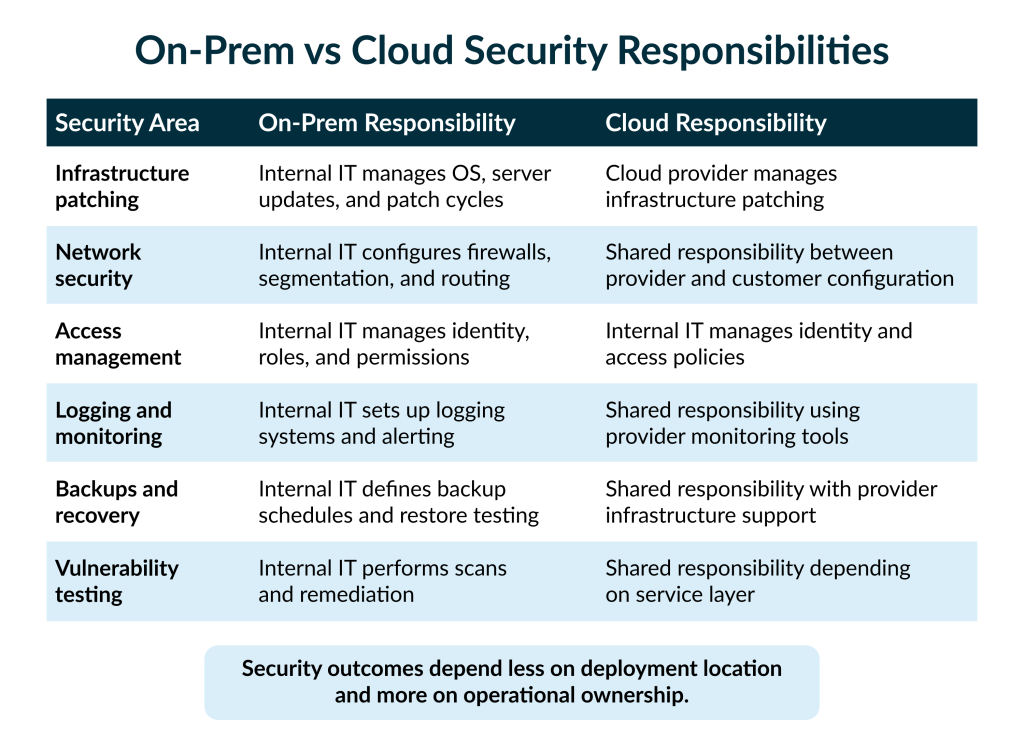
What matters more is how the system is operated day to day. Real security depends on who patches systems, who monitors activity, who manages keys and access, and who responds when something breaks.
In other words, the real question is not on-prem versus cloud. It is operational security ownership.
This article compares both deployment models through a practical security lens to help teams evaluate risk, responsibility, and operational capacity.
What Security Actually Means in Deployment Decisions
Security in deployment decisions is rarely about where servers sit. It is about how the system is operated and protected.
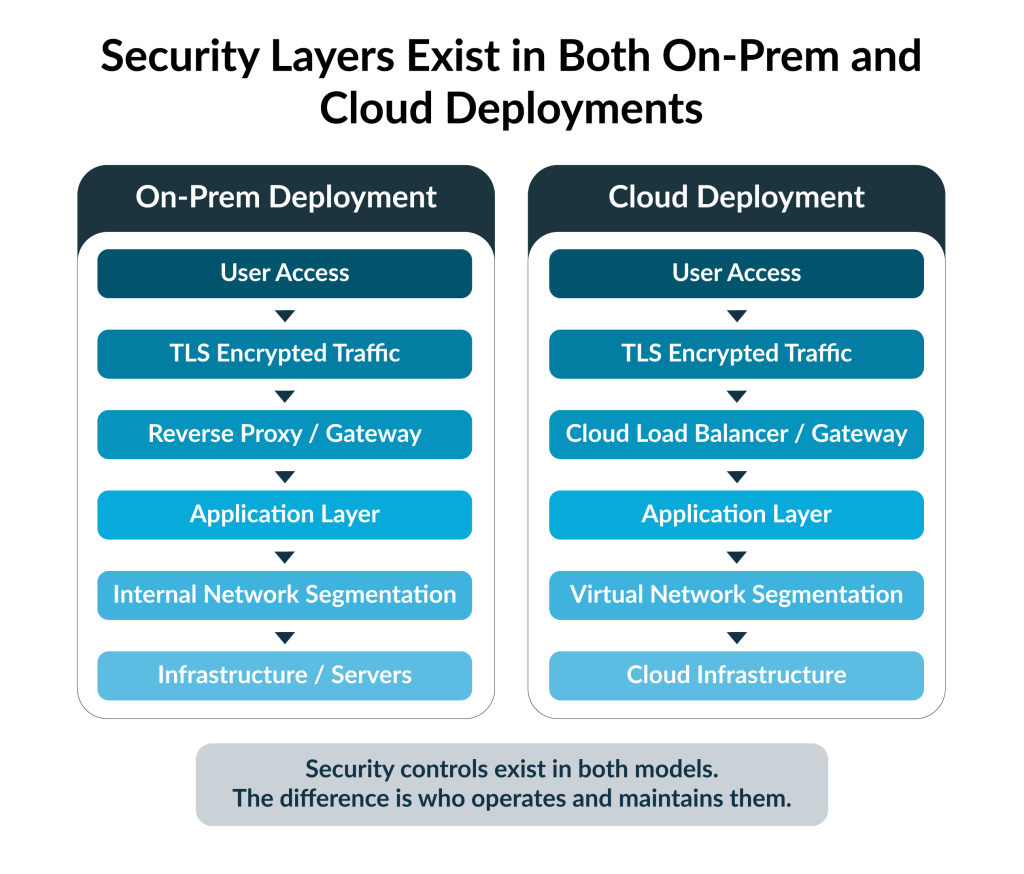
Several operational controls determine whether an environment is actually secure. These include TLS encryption for all traffic, reverse proxy architecture to protect application endpoints, and network segmentation to limit internal exposure. Strong environments also rely on identity-based admin access, centralized logging and monitoring, and well-tested backup and recovery procedures. Regular vulnerability testing completes the picture by identifying weaknesses before they become incidents.
These controls apply to both on-prem and cloud deployments.
Either model can be secure when these practices are implemented consistently. Both can also be dangerously misconfigured.
Security outcomes ultimately depend on operational discipline and monitoring, not simply the choice of deployment model.
How On-Prem Security Typically Works
On-prem deployment gives organizations maximum control. It also assigns them full operational responsibility.
Typical architecture
- Hosted within corporate infrastructure
- Protected by internal firewalls
- Accessed through VPN or internal gateways
Security strengths
- Full control over infrastructure and configuration
- Data remains within the internal network perimeter
- Easier alignment with internal compliance and regulatory policies
Operational realities
- Internal teams must manage system and OS patching
- Monitoring, alerting, and incident response must be maintained internally
- Backup and recovery procedures must be defined and regularly tested
On-prem security depends heavily on operational maturity. Strong infrastructure teams can operate these environments very securely. Weak processes, however, can introduce risks that remain invisible until something fails.
How Cloud Security Typically Works
Cloud deployment shifts much of the infrastructure security responsibility to the provider, but it introduces a different operational focus.
Typical architecture
- Hosted within a cloud environment
- Protected by managed infrastructure security controls
- Accessed through secure public or private endpoints
Security strengths
- Automated patching and infrastructure hardening handled by the provider
- Provider-level monitoring, resilience, and redundancy
- Built-in encryption capabilities and high availability
Operational realities
- Identity and access controls must be tightly managed
- Configuration mistakes can unintentionally expose services
- Logging, monitoring, and alerting still require active oversight
Cloud security relies less on physical or hardware control and more on configuration discipline. Organizations that manage identity, access, and monitoring carefully can achieve very strong security outcomes in the cloud.
Where the Real Security Work Happens
The most important security controls exist in both on-prem and cloud environments. What changes is not the controls themselves, but how they are implemented and maintained.
Key operational controls include:
- TLS encryption for all traffic to protect data in transit
- Reverse proxy patterns that shield internal services from direct exposure
- Network segmentation to limit lateral movement inside the environment
- Key-based administrative access instead of shared credentials
- Centralized logging to monitor activity and detect anomalies
- Regular backups with tested recovery procedures
- Vulnerability scanning and testing to identify weaknesses early
These controls form the foundation of secure deployment.
The difference between secure and insecure environments rarely comes down to where servers sit. It comes down to how consistently these controls are implemented, maintained, and monitored over time.
A Practical Scorecard for Choosing
Deployment decisions become easier when teams evaluate them through a consistent framework. Instead of debating philosophy, IT teams can compare on-prem and cloud models across a few practical dimensions.
Key factors to evaluate include:
- Infrastructure control
- Operational workload
- Patch management responsibility
- Monitoring ownership
- Scalability requirements
- Compliance alignment
Each organization will weigh these factors differently. Some prioritize maximum control and direct oversight. Others prioritize operational efficiency and faster scaling.
Organizations with strong internal infrastructure teams often prefer on-prem environments, where they can manage every layer directly. Organizations focused on speed and operational simplicity often lean toward cloud deployments.
“There is no universal ‘right answer’. The right choice depends on an organization’s risk tolerance, operational capacity, and ability to maintain security controls consistently over time.”
Conclusion: Security Is an Operating Model
Security decisions are ultimately operational decisions.
Both on-prem and cloud environments can be secure when they are managed properly. What matters most is not where the system runs, but how it is operated. Strong security depends on clear ownership of responsibilities, consistent monitoring of activity, disciplined patching practices, and tightly controlled access.
The most secure environment is the one your team can operate responsibly every day.
At SplashBI, we support both deployment models because enterprises operate under different risk models and infrastructure realities. Our goal is not to push a single deployment approach. It is to ensure that security works reliably in whichever environment your organization chooses.
Ready to define your strategy?
Deciding between on-prem and cloud involves many variables. We can help you navigate the technical and operational requirements.
Click here to talk to a deployment expert and know your optionsGet a personalized consultation based on your specific needs.